Windows DriveStrike Mass Deployment Guide
DriveStrike can be deployed by IT administrators via mass deployment mechanisms (e.g., via Active Directory GPOs, or via a third-party asset management system). This document provides an overview on how to deploy DriveStrike via these mechanisms. If you are deploying on Linux please see our Linux mass deployment guide. For detailed instructions on DriveStrike mass deployment, please logon to your DriveStrike account and go to the Install page – a link to our deployment documentation can be found there.
Step 1: Create a mass deployment token
Since mass deploying DriveStrike has the potential to impact a large number of devices, we require IT administrators to create their own deployment token within DriveStrike. This process is very simple, and can be completed in just a few seconds.
The mass deployment token will not expire, so you can use it to deploy DriveStrike to machines in the future as well. If you ever find that this token has become compromised, please contact DriveStrike Support.
Step 2: Configure your deployment mechanism
You will need to configure your deployment mechanism to run the DriveStrike installer with custom parameters. More detail can be found in the mass deployment guide found at https://app.drivestrike.com/doc/massdeploy/
Step 3: Test your deployment
To confirm you have the proper mass deployment token, use a test machine (or VM) and install using the instructions above.
Note – on Windows, you can run the DriveStrike installer and provide the mass deployment parameters mentioned in the previous section. Since no UI will be displayed, you can use the Windows Task Manager to monitor the state of the setup.exe process.
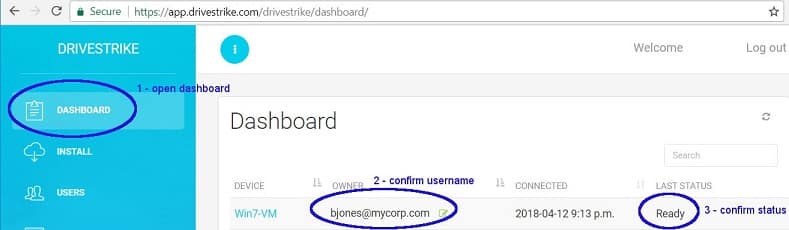
Once the deployment process completes, log into the drivestrike.com website, navigate to the Dashboard page, and confirm that you see the expected device owner, with a device that shows the “Ready” state:
After you confirm the machine installed correctly, you can uninstall DriveStrike from the machine and delete the device from the DriveStrike website.
Next, you may wish to push the DriveStrike installer to a test machine (or VM) via your preferred application deployment mechanism, to confirm the software delivery channel.
Step 4: Deploy to production machines
When you deploy to production machines, you can always monitor the status of your deployment through the drivestrike.com Dashboard page. Machines to which DriveStrike has been deployed successfully will be visible in the Dashboard and show a status of “Ready.”
Appendix A – Deploying via GPO or SCCM
IT administrators may choose to deploy DriveStrike via a GPO pushed through Active Directory, or using a centralized software management system such as Windows SCCM or ivanti.
A straightforward way to deploy DriveStrike in this fashion is to push a PowerShell script that installs DriveStrike with the appropriate parameters. To do so, create a PowerShell script similar to the following, and save it to your desktop. Note that this file must have a file extension .ps1. Provide appropriate values for your mass deployment token. Details on our sample script can be viewed once logged into your DriveStrike account.
- Create a new GPO and link it to the desired Organizational Unit (OU).
- Edit the GPO, then open Computer Configuration / Policies / Windows Settings / Scripts.
- In the Computer Configuration case, right-click on Startup and choose Properties. In the User Configuration case, right-click on Logon and choose Properties.
- Select the PowerShell tab.
- Click “Show Files” to open an Explorer window to a location specific to this GPO, then drag the PowerShell script you created earlier into this Explorer window.
- Click [Add], then [Browse], and choose the script file you just copied in.
- Click [OK], [Apply], or [Close] to exit your way out of the edit dialogs.
- The installation script will run when the computer is restarted, and install DriveStrike if it is not already installed.
- As you deploy DriveStrike throughout your organization, you can trigger installation on new OUs by right-clicking, choosing “Link and Existing GPO…”, and then choosing the GPO you created previously.
A common desire is to install DriveStrike via a user-based Logon script instead of a computer-based Startup script, to avoid the need to reboot. The challenge with this approach is that the DriveStrike installer requires elevated permissions to run. When a user that lacks permissions to elevate processes logs in to Windows, the installer will still run but will prompt for elevation credentials. Having said that, if the users in your target OU have permissions to elevate processes, then deploying via a per-user Logon script may be successful.
Appendix B – Installation Notes
.Net Installation
The DriveStrike installer depends on the .Net runtime version 4.6.2 or later. When the installer is launched, it first queries the .Net runtime versions present on the machine, and then downloads and installs an appropriate .Net version if necessary. Note that this requires that target machines have internet access.
If mass deployment parameters are passed to the DriveStrike installer, the .Net installer is launched in a “quiet” mode that shows no UI.
Silent Installers and the UAC
The /verysilent flag passed to the DriveStrike installer is appropriate for unattended installations, as long as the installer process is launched with appropriate admin privileges. The installer requires elevated permissions, and will query the user for such if it was not launched with elevated privileges.
